
The contest gives you a chance to compete with some of the best technical minds in the country and stand a chance to win exciting prizes!

Participants chose their desired topic from the following list:
Cloud is the new way of achieving elastically scalable, self-service computing and applications. Growth of ‘Cloud Infrastructure’ is helping organizations to adopt ‘Cloud-first’ strategy by moving their on-premises applications safely to the cloud. Cloud is enabling organizations to focus on their core business by minimizing expenditure on computer infrastructure and maintenance, without compromising on computing requirements of their organizations. It has firmly established itself as the new normal for enterprise IT and business. Ranging from startups to enterprises, it is difficult to find an organization that does not have its workload on the cloud.
Some of the areas of interest for students to work on innovative projects:
The convergence of cloud and mobile computing will continue to promote the growth of centrally coordinated applications that can be delivered to any device. Cloud is the new style of elastically scalable, self-service computing, and both internal and external applications will be built on this new style which employs Software as a Service (SaaS) model. In the near term, the focus for cloud/client will be on synchronizing content and applications across multiple devices and addressing application portability across devices. Over time, applications will evolve to support simultaneous use of multiple devices. In the future, games and enterprise applications alike will use multiple screens and exploit wearables and other devices to deliver an enhanced experience. Example: As the need for cloud based apps and services continues to grow, there will be a need for a development model for these applications and services, which will support the cloud based software development lifecycle.
Microservices
For simple and limited scale applications monolithic architecture is still relevant. Modern cloud application that requires agility scale and reliability, Microservices Architecture offers great promise. A Microservices application is composed of independent components called ‘Microservices’ that work in concert to deliver overall functionality of the application. Unlike monolithic applications, Microservices applications enable the separation of application from underlying IT infrastructure.
Students are encouraged to propose projects on Cloud Applications and Microservices. Projects should be complete in all features and demonstrable while keeping the data secure during rest and during transit.
Some of the areas of interest for students to work on innovative projects:
Depending on the security landscape and attack vectors, security hardening is important for various use-cases of technology implementation. A range of security technologies exists for various domains and their use-cases. Enhancements/improvements and innovations in these security use cases for specific implementations are also required to keep up with the changing landscapes and postures.
Software innovations around security technologies that can handle various use cases are welcome. You can also consider hardware-assisted security models too as part of PoC. Some of the areas of interest for innovative projects, which also meet the standards/compliances such as, HIPPA, GDPR, ISO 27001, or PCI DSS, are:
Multi-modal biometrics is fast becoming the go-to security option for enterprises that want to offer the most secure and convenient authentication for their customers. Multi-modal authentication benefits the enterprise in specific ways. It vastly improves the customer experience with no cumbersome passwords to remember. It also improves the security of traditional authentication and prevents hacking and data breaches. We are looking for new ideas around it for use cases such as, electronic Know Your Customer (eKYC), user identification/verification, image recognition/verification, or design ideas that can be used across multiple industry/business domains ranging from financial, transportation & logistics, social services, safe cities and life sciences & healthcare. All the use cases must also consider meeting the standards/compliances such as, HIPPA, GDPR, ISO 27001, or PCI DSS.
Some use cases are as follows:
Fifth Generation Networks (5G), the Internet of Things (IoT) and Edge Computing are essential infrastructure enablers for a range of new business and technology developments. It is often termed as Industry 4.0 that covers areas like autonomous vehicles, smart city grids, e-health, automated factories, mobile content streaming and data analytics. This marks a significant step on the journey to genuine digital transformation.
5G and Edge computing, along with IoT platforms and frameworks, are key enablers for Industry 4.0. Without these, there will be network problems, not only in providing connectivity for the 20 billion IoT devices, but also in transferring and processing the huge volumes of data that will be generated. The problems are not just about bandwidth. Different IoT solutions will have different network requirements. Some devices, like autonomous vehicles and medical equipment demand absolute reliability where low latency will be critical. Other use cases will see networks having to cope with a much higher density of connected devices than seen from traditional 4G networks. The promise of 5G, the development of Network Function Virtualization (NFV) and the ability to process some transactions and store data near to the source of that data, i.e. at the Edge, will be key determinants of the success of Industry 4.0.
Use cases:
Digitization and cheap storage has led to a myriad of data - both structured and unstructured - which we call Big Data. This, along with advances in Machine Learning and Deep Learning, has enabled us in two primary ways. One is to be able to understand the complex interrelationship of data, thus helping in deriving hidden patterns in data. It enables us to make better business decisions like predictive and prescriptive analytics. The second is to automate processes and bring in intelligence into digital things. With faster data management and computing technologies available, it has also become imperative to come up with intelligence based on data and information that is real-time or near real-time. The use of analytics to come up with cognitive (human-like) and intelligent interactions in a B2C scenario is becoming more prevalent. This helps in better personalization and reduces operations costs for businesses. Other than customer-generated data which includes open data sources and the dark internet, sensors, chips, machines and other digital devices generate time series/stamped data which also interacts with each other for various outcomes. IoT analytics deals with this stream of analytics primarily.
We are interested in students developing solutions in each of the areas talked about above. Predictive Maintenance solutions for IoT equipped devices, Cognitive interfaces like Chatbots and contextual text miners using NLP, Deep Learning based Picture and Video recognition solutions which can go beyond face recognition and can identify from other pictures like X-Ray scans, etc. Bayesian Network based Anomaly Detection and outcome predictors, Neural Network driven decision and automation management systems are examples of some of the solutions and capabilities being looked at and developed by us at Unisys. We use the latest codebases and platforms to build our solutions on the Amazon clouds and other APIs and codebases provided by Python, Google APIs, etc.
Also, look at HyperAutomation – AI + Automation
With mobile phones becoming more powerful, there is increased emphasis on serving the needs as well as harnessing the power of the mobile user in diverse environments, as opposed to focusing on devices alone. For example, backend processing for data personalization and patternization, and use of these patterns to create more effective and efficient context sensitive information sharing for the end user’s benefit. Students are encouraged to propose projects which are based on the concept of Computing Everywhere.
Computer Scientists around the world are doing extensive research in different areas. Few of these technologies may emerge and change computing in the near future such as Blockchain, Cognitive Computing, Application Defined Data Center, Microsegmentation and Fintech (Financial Technology). We are looking at submissions that come up with innovative ideas in these areas, addressing various aspects of implementation and usage.
Ubiquitous embedded intelligence combined with pervasive analytics will drive the development of systems that are alert to their surroundings and able to respond appropriately. Context-aware security is an early application of this new capability, but others will emerge. By understanding the context of a user request, applications can adjust their security response and how information is delivered to the user - significantly simplifying an increasingly complex, computing world.
We encourage students to submit and work on these potential technologies.
Be it large, small, or medium sized, every business is now talking about cloud computing. Airports are no different. Fundamentally, airports are like clouds that provide a shared network, shared check-in systems, baggage reservation systems, and other IT infrastructure that is leveraged by all airlines operating in and out of the airport. Airport operators are under constant pressure to maintain a state-of-the-art IT environment, but find themselves year-on-year with shrinking IT budgets. We are interested in papers that explore the various solutions in an airport that can be part of a cloud and intelligibly analyze the tangible and intangible benefits that would accrue by implementing such solutions.
Virtual Simulation
Virtual reality simulation is the use of 3D objects and environments to create immersive and engaging experiences. Transport products such as Airline passenger service, Airline cargo, Airport operations, etc. that deal with the multiple subjects, their movement, synchronization of information, geo-location, subject identification, etc. can find numerous usage with the virtual simulation. Its usage into product development are immense, they not only help in discovering the hidden business cases, which can be incorporated into the product, but also can play an important role during product testing with better visualization.
Software Telemetry Service
Telemetry includes capturing, processing and interactive display of software usage trends. Data regarding an application's usage along with user's profile (keeping PII - Personally identifiable information - outside) is gathered from multiple channels. All ingestion points contribute data towards a single repository. Analytics is developed against this data repository to understand usage trends based on different personas which allow the product team to understand the impact areas for further focus and derive business insights.
Students are encouraged to work on any transportation domain projects.
Cloud Computing is still in the realm of research and development. Organizations/ Universities are spending money and effort to achieve newer breakthroughs. Students are encouraged to submit projects on emerging cloud technologies related to following research topics:
IT security analysts are being flooded with data streaming from a wide variety of sensors, deep packet inspectors, SIEM tools, etc. This data is usually presented in the form of log events, status messages, and security alerts, and quickly becomes overwhelming for human analysts to understand. While machine learning and AI can help make some sense of the data by creating models of expected behavior, it still requires an analyst to dive deeply into the data to investigate the anomalous activity, or to resolve conflicting alerts.
Similarly, IoT sensors generate prodigious amounts of real-time data that needs to be ingested, processed, and examined against operational norms.
The human visual system has evolved over millions of years to detect and focus on anomalies, while ignoring mundane recurring patterns. For example, one can arrive to work with no recollection of the morning commute. Yet, if something unusual occurs in our visual field, it stands out and instantly focuses our attention.
We are looking for research projects that investigate how to leverage this uniquely human ability, combined with state of the art VR/AR tools to better detect, analyze and remediate security and operational issues buried in masses of normal security and/or IoT data.
Agile methodologies (DevOps) are popular in the industry with rapid prototyping and release. Every organization with a DevOps framework should be looking to shift towards a DevSecOps mindset and bringing individuals of all abilities and across all technology disciplines to a higher level of proficiency in security-from testing for potential security exploits to building business-driven security services. The integration of security concepts into this framework is usually done haphazardly or not at all. What was usually done at the end of the development process now has to be integrated back into the process – probably with tools and automation. How can we ensure security in everything as we sprint and scrum?
Some of the areas of interest on this topic are
Integration platform as a service is a cloud service that provides a platform to support applications that involve a combination of data sources and cloud-based applications and others. It is aimed at integration and governance of on-premise and off-premise applications, cloud applications, SOA applications both within, outside and across organizations.
Companies use these to strategic advantage in positioning their products on the cloud space leveraging iPAAS thereby enhancing their offering potential.
The direction in which the industry is moving indicates that many products, eco systems should co-exist and together solve a business problem of an enterprise given the modernity of requirements thus making iPAAS as a critical alternative to traditional integration middleware.
Integration Service for multi cloud platforms is an important area of interest for the contest.
Blockchain is a distributed database system - this means, instead of storing files on a single computer, information is stored across millions of computers all over the globe. It gives end-users the power to control their personally identifiable information. We are increasingly observing a wider range of use cases for blockchain across small and large-scale applications.
There are various applications in which Blockchain can provide a cutting edge to the traditional technologies because of its immutable nature, faster settlement and decentralized technology. Unisys invites students to provide innovative solutions in the fields of
Today, IT is a critical business enabler. The IT ecosystem in an enterprise is a combination of in-house applications, cloud based applications and vendors. The challenge any CXO faces is the lack of an integrated view of services running across these complex environments.
Students are encouraged to come up with a solution that provides a real time view of existing services and health of their underlying infrastructure. The ask is to create an innovative dashboard that is visually insightful and provides intuitive insights on the next best action to any CXO leveraging analytics. The expectation is to create a dashboard wireframe which provides a drilled down view of services.
Examples:
We will update the content shortly.
We will update the content shortly.
One of the most important aspects while enrolling in the biometrics of a user is to be able to validate the user against his/her document identity. This is becoming imperative in the current times where cyber frauds are on the rise.
Currently, there is an automated process for a very selected set and type of documents and all other validation needs to be done manually. The current COVID situation has demanded a lot of contactless and automated services that can help reduce the number of touchpoints and thereby mitigate the risks associated with the pandemic.
Document detection has become a very challenging process as there are a plethora of document types across the globe. Having a repository of all the possible templates that a product can work with is a very difficult task if it has to be done manually. If we do not have templates, then we cannot efficiently use OCR techniques to extract information from these documents and perform the next steps.
Another challenge is that these documents also go over transformation over a period of time. For example, we still have valid passports that are hand-written versus the new ones that are machine written. Also, the fields for the same set of documents also undergo change.
The solution to this problem statement is to come up with innovative solutions using AI/ML to train models that can automatically templatize from a set of documents. These templates can then be stored into the template library maintained by the product and used for any future detection of such types of documents.
The teams are expected to use their own set of identity documents for this effort. There are online test sets available from multiple sources and you can use Indian documents as well like Aadhaar or PAN or DL or Passport. Once you have the service ready for evaluation, the Unisys team will take it and run it against our internal set of documents to ensure that it works as expected and creates templates.
Consent capturing is a very important aspect of this solution as it deals with the user’s private demographic details. The solution needs to adhere to all the data privacy regulations that are in force at the moment as well as have an implementation of “Right to be Forgotten”
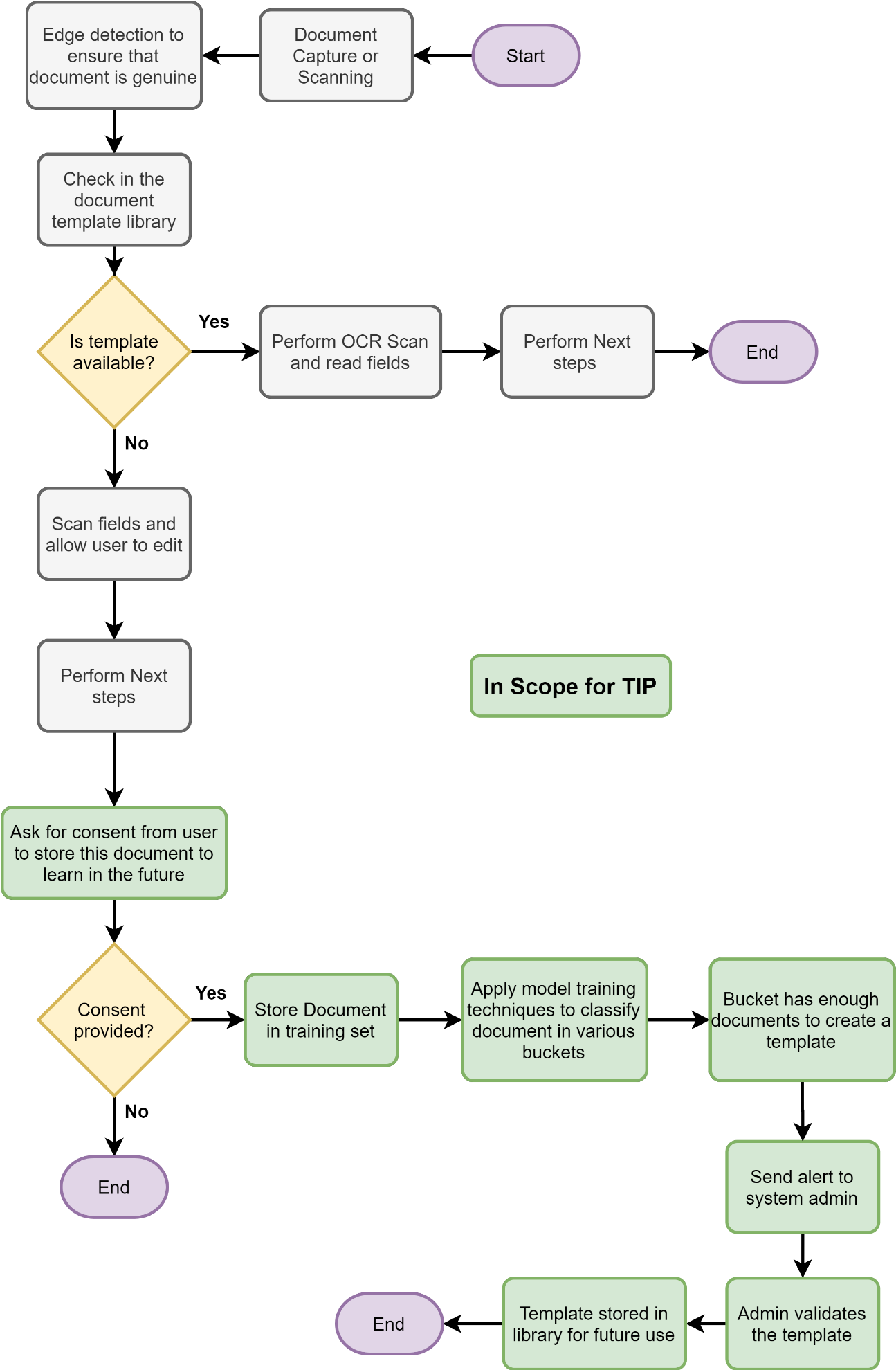
A flow diagram for the same is shown
AI, ML, NLP powered assistants like Alexa, Google Assistant, Cortana, Siri, etc. are now part of our daily lives. We wonder if there was one such AI, ML, NLP powered assistant for associates at any organization that would make their lives easier. Every associate spends some amount of time in a day on certain activities like:
The list goes on and on. The point here is, we all spend a small amount of time on each such activity and over the period of weeks or months or year, which accumulates to large amount of time per associates. When we analyze this across the organization then the impact is so large that we cannot continue to ignore it.
UNA - The master AI System will be executing as @una.mother and each UNA Agent deployed on the associate's desktop/laptop/mobile will be running as @una.associate e.g. @una.sanket for me. Each @una. is a child of @una.mother and will be directly communicating with @una.mother. @una. child nodes will be capable of direct communication with each other as well. This makes it a perfect distributed computing system that can work like having one mind, just like a hive.
UNA can be developed as a modular, pluggable, scalable, programmable and trainable system.
Some use-case of UNA:
Large public spaces like smart cities, sports complexes, airports, rail stations, multi-modal hubs and religious places witness very large crowds with a need to recognize crowd patterns and develop heat-maps towards delivering superior customer service and achieving operational excellence.
As we move to a contactless future, it is inevitable that many organizations will switch to contactless biometric scanners (such as face and iris recognition) to remove points of contact in many processes like entry into restricted office spaces. This will increase the number of matches that have to be performed daily, and the list of people to be identified at a certain outlet/location of an organization more or less ends up being the same subset of people every day.
With the above scenario in mind, we can optimize the secure retrieval and comparison of biometric information from the cloud enclave by securely caching a slice of the relevant information at edge devices in the building. Therefore moving the biometrics retrieval and processing overhead to the edge and significantly reducing latency, cloud computation and storage retrieval.
This also opens the door to various edge analytics solutions to take actions based on biometric verifications with low latency, and also removes the dependency on an internet connection to perform matches on already cached entities, allowing for higher availability
The edge enclave intelligently caches the biometric data that are most frequently required on a priority heuristic basis and performs the biometrics processing right there at the edge. If the identity is cached already or in the case where it's not yet cached, the system delegates this task to the cloud biometrics engine. The biometric data is synced and retrieved from the secure biometric store in the cloud.
Unisys’ biometric capabilities are designed to establish trust and enable irrefutable access, whether to a building, an airplane, or a protected asset in the cloud. We don’t use images "scraped" from social media or large databases, but rather register users requiring authentication. This is a fundamentally different value proposition and use, and one that keeps us on the outside of the legitimate concerns being raised.
The solution designed must comply with all data privacy regulations like GDPR and HIPAA compliance. No data/biometrics can be taken without any consent from the user.
Participants chose their desired topic from the following list: